Ransomware Attacks: A Growing Threat to Government Entities
The fast-paced digitalization of different aspects of life has not left government agencies behind. Today, various public sector services such as applying for permits, filing cases, recording statements, renewing a driver’s license, etc., can be completed online. This has led to cost savings, optimal efficiency, improved flow of information, enhanced transparency, and more.
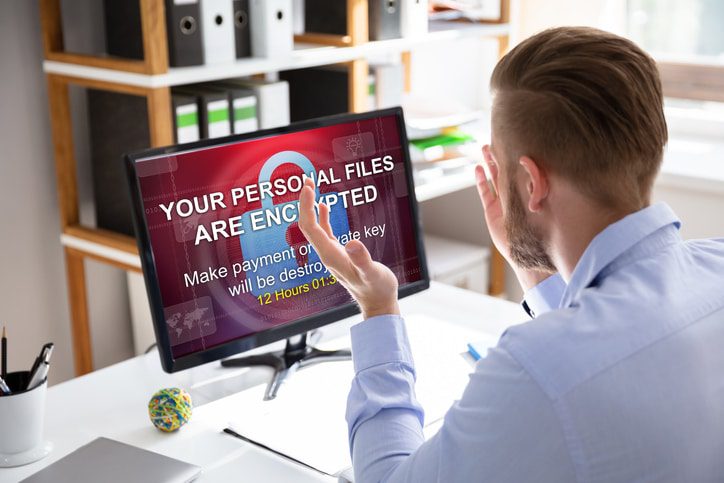
However, there’s the flip side of the coin that’s not entirely pleasing. As government databases continue to enjoy increased online presence and usage, they equally position themselves as easy targets for ill-intended users. Cyberattacks on federal agencies are a significant cause for alarm, as data breaches have increased in frequency, complexity levels, and economic implications over the years.
Not long ago, the DC police department got hit by an apparent extortion attack by a Russian-speaking ransomware syndicate who claimed to have stolen different sets of sensitive data. That’s just one of the 26 government agencies that have been hit by ransomware attacks so far, and unless immediate action is taken, the trend may only get worse.
So the big question is, how can government agencies and other private sector organizations avoid becoming the next victims? In this article, we share the best tips for acting proactively to prevent ransomware attacks. So let’s dive right in!
Actionable Tips for Preventing Ransomware Attacks
Before we get to the details, it is critical to note that these tips apply to federal agencies and every other organization or business. So here we go!
Prioritize Security Awareness Training
Security awareness training or SAT is one of the best tools for preventing any form of cyberattack. How so? The people within your organization are the greatest weak link between sensitive data and cybercriminals. So training them on what and what not to do is half as good as getting the job done.
The best SAT program should train users on all the risks that stand in their way when using the internet to complete tasks in the office or at home. The awareness training helps users understand what cyber threats look like, the best practices they should implement to stop them, and the actions they should take should a risk occur.
SAT solutions also encompass simulated phishing technologies. Here, the trainers or admins create simulated phishing emails and distribute them to employees to gauge how effectively they can uncover or detect ransomware attacks. Simulation is an impeccable way of helping organizations and agencies determine their security preparedness and pinpoint specific users that require more awareness training to help prevent ransomware all-across.
Invest in Data Backup and Recovery Solutions
If your organization or agency suffers a ransomware attack and your sensitive data gets compromised, the best way to prevent further loss and minimize downtime is restoring the data. Backing up data on multiple spots, including the cloud, local disk, and the primary storage area, is a wise move that will ensure you remain protected in case of a cyberattack.
In particular, cloud data backup and recovery solutions are, by far, the best platforms to preserve your data’s safety and guarantee its restoration should the worst happen. The data backed up in the cloud is always available for quick and secure retrieval anytime and can even be integrated with endpoint devices or existing cloud-based applications. The key takeaway here is that cloud data backup and recovery solutions are instrumental in remediating ransom attacks.
Reevaluate the Resilience of Your Third-Party Vendors
Most businesses and government institutions partner with third-party vendors who provide particular products or services to customers or users on their behalf. These vendors usually have access to sensitive data such as employee information, consumer behavior, and more. The big question is, how committed are they to protecting your organization’s sensitive data against unauthorized access? And are they capable of recovering quickly from difficulties like network downtime or power outage?
Those are the questions you should be seeking answers for when reevaluating the resilience of your third-party vendors. 3rd party partners are one of the weakest links for many entities and organizations, and federal entities if the recent trends are anything to go by. Cybercriminals are now switching their focus towards the vendors as an easy way to victimize businesses and government entities.
Luckily for the Department of Defense, it requires all its contractors to complete certain cybersecurity maturity levels before getting the go-ahead to compete for federal contracts. This is a massive step towards cyberthreats prevention as the department guarantees that all its unclassified information will remain protected in the hands of third-party partners.
But since private sector organizations and other government entities may not have a clear-cut cybersecurity assessment program, reevaluating their partners’ and suppliers’ resilience may be their best shot at uncovering potentially harmful blind spots.
Install a Rock-Solid Endpoint Antivirus Security
Having an impenetrable endpoint antivirus security is one of the best proven ways of preventing ransomware attacks. When anti-virus solutions are installed on endpoint devices, they block any malware that may attempt to infect your systems. Anti-virus solutions also give administrators a heads-up when the system has been compromised. Plus, they ensure that the most recent updates have been installed.
But that’s not even the best part. Endpoint antivirus security also prevents users from completing malicious downloads and even alerts them when they’re about to visit a risky site. Let’s face it, though; we can’t state that these solutions are 100% effective because cybercriminals are always working round-the-clock to innovate new techniques for getting malware past the security installations. However, there’s no denying that endpoint security is a great step towards ransomware attack prevention.
How Can TREYSTA Technology Management Help?
Ransomware attacks are 100% preventable, and it’s high time government entities and businesses rose to the occasion to elevate their cybersecurity posture. The fastest and most effective way to achieve that feat is by implementing the above steps. These include prioritizing awareness training, acquiring data backup and recovery solutions, reevaluating your partners’ resilience, and installing endpoint security.
More importantly, you want to partner with a reliable cybersecurity professional to have access to expert-based assistance and resources. That’s where we come into play! TREYSTA is an industry leader in cybersecurity matters, and we take pride in helping businesses achieve security compliance while keeping cybercriminals at bay. We do this by offering 24/7 systems monitoring, help desk support, security awareness training, data backup and disaster recovery, among other solutions.
Schedule a no-obligation consultation with one of our experts today, and let us help set you apart from the competition through enhanced security, productivity, and cost savings.