In today’s fast-paced world of technology, businesses need a secure and preferred payment method to handle financial transactions efficiently. That’s where ACH payments, or eChecks, come in. ACH offers superior safety, cost-effectiveness, and convenience compared to traditional paper checks. Here are 3 key benefits:
- Robust Security Measures:
ACH payments prioritize security through encryption, data protection, regulatory compliance, and multi-factor authentication. Your sensitive financial information remains confidential, reducing the risk of data breaches and unauthorized access. - Streamlined and Efficient Process:
ACH payments automate the payment workflow, reducing the risk of errors and saving time. Funds transfer faster than with traditional methods, enabling better control of daily cash flow. - Cost-Effectiveness: ACH payments involve lower transaction fees and reduce overhead costs by eliminating physical checks, postage, and manual processing. This cost advantage translates into significant savings, especially for businesses processing a large volume of transactions.
At TREYSTA, we prefer ACH payments for their secure nature, streamlined processes, and cost-effectiveness. ACH payments generally involve lower transaction fees for TREYSTA, compared to other payment methods such as credit cards or wire transfers. Keeping TREYSTA’s costs down allows us to pass those savings on to our clients and that is why we offer ACH payments at no cost.
Stay ahead of the financial innovation curve and focus on what your business does best with ACH payments as your secure and preferred payment solution. Please reach out to our Business Manager, Debbie, if you have any questions regarding setting up ACH payments in our payment portal.
Keep Reading: The Secure and Preferred Choice: 3 Benefits of ACH Payments

Did You Know?
86% of small businesses are considering replacing traditional phone systems with cloud-based communications like VoIP.
Voice over Internet Protocol (VoIP), also called Hosted Voice, is a technology that uses the internet to make and receive phone calls. Instead of using traditional telephone lines, VoIP converts voice signals and sends them over digital networks. This can be done using a VoIP compatible business phone, your mobile device, or even through your internet browser!


Business phishing scams are targeted attacks that aim to steal sensitive information. These scams are designed to target businesses, their employees, and customers. Learn 6 tips how to protect your business.


By using just a username and password to login, it leaves your account vulnerable to a cyberattack. In fact, 1 in 2 internet users had their accounts breached! It’s more important than ever to protect your accounts. Learn 5 reasons you need to use MFA.
Check Out This Month’s Help Desk Stats!
2
Minutes Avg. To Respond
89%
% Responded < 5 Minutes
525
Tickets Closed


Team TREYSTA has had the pleasure of stepping outside the confines of our offices recently by actively engaging in volunteer work and attending local events!
Through volunteering initiatives and active participation in local events, we not only get to support local businesses but also experience the joy of giving back. These experiences deepened our appreciation for the vibrant and diverse community that surrounds us!
Team TREYSTA will also be attending FunFest on Friday June 9th from 3pm to 7pm at the Gettysburg Rec Park. For more information, please visit www.adamslibrary.org/funfest!
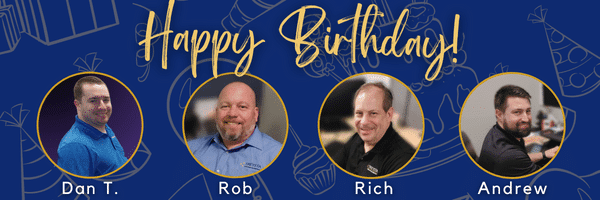
Happy Birthday!
These guys have a birthday coming up in June…
Happy birthday to you and thank you for all that you do!
TREYSTA technology management
Your Trusted Technology Team!
“Trust is built with consistency.” -Lincoln Chafee